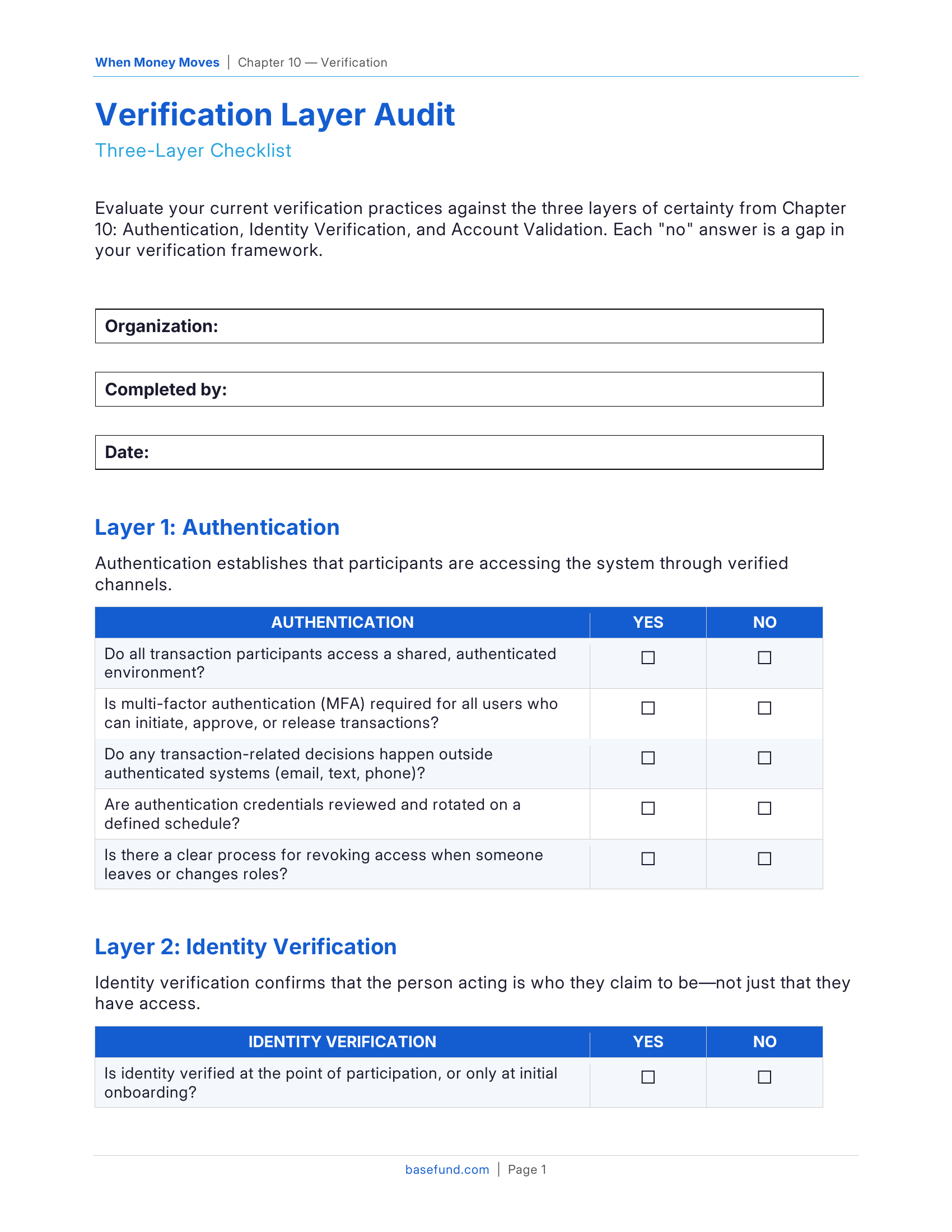
Verification Layer Audit
Three-Layer Checklist
Editable Word document (.docx) + print-ready PDF
"How many layers of verification stand between your organization and a fraudulent transaction?"
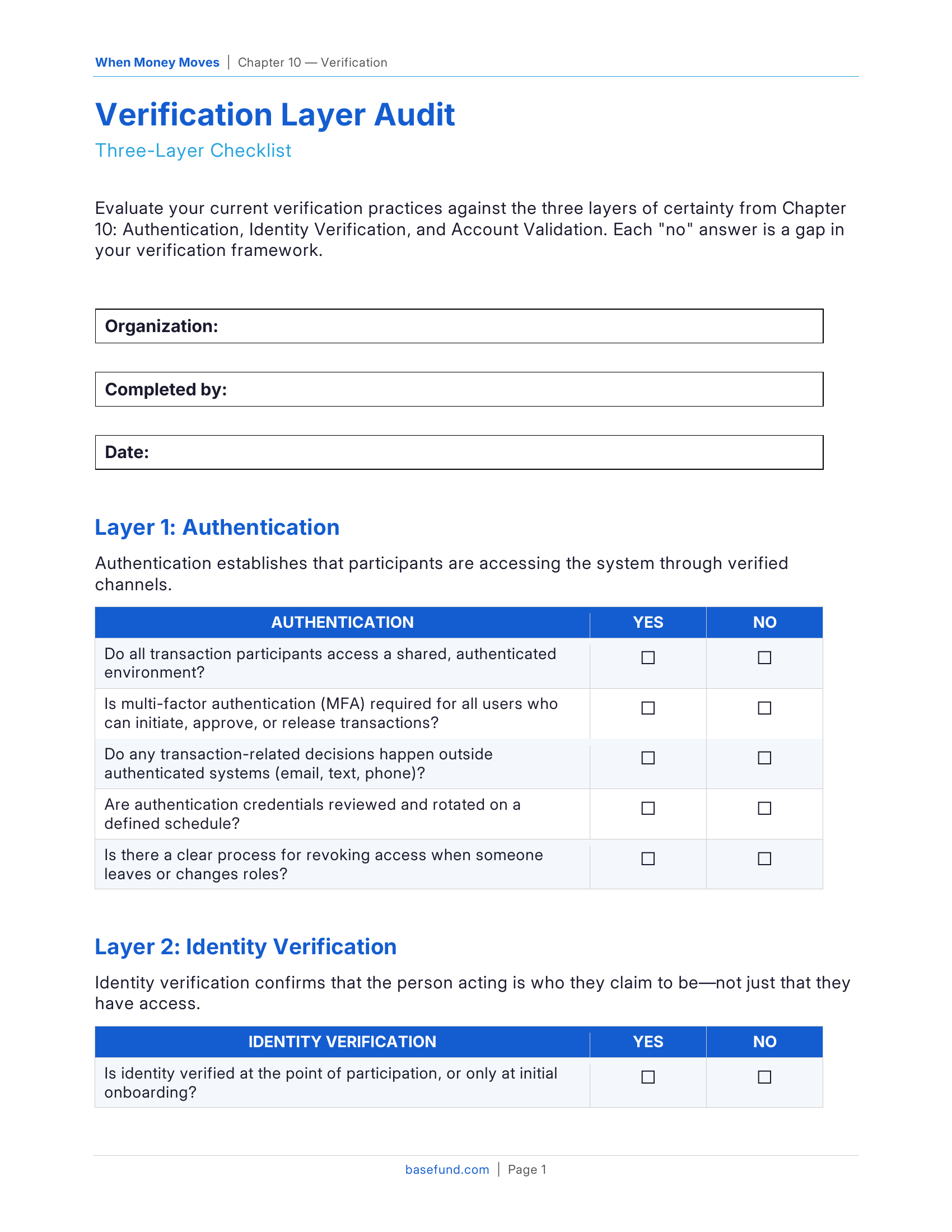
Three-Layer Checklist
Editable Word document (.docx) + print-ready PDF
"How many layers of verification stand between your organization and a fraudulent transaction?"
What You'll Get
How It Works
Who It's For
Treasury managers, risk officers, IT security teams, and anyone responsible for ensuring that transactions are verified before funds move.
The Key Insight
Most organizations have some verification in place, but it's rarely layered consistently. Authentication might be strong while account validation is weak. This audit reveals which layers are protecting you.
Enter your work email to download the PDF and editable DOCX.
This resource is a companion to Chapter 10: Verification of When Money Moves.
The chapter provides the full framework — this tool helps you apply it. Get the Book